Below you will find Guidance Documents released by the NCSC.
-
National Cyber Emergency Plan
Then National Cyber Emergency Plan (NCEP) sets out the national approached for responding to serious cyber security incidents that affect the confidentiality, integrity, and availability of nationally important information technology and operational technology systems and networks.
-
Research and Innovation Priorities
The National Cyber Security Centre (NCSC) plays a central role in improving the State’s cybersecurity resilience. As part of that work, we engage on an ongoing basis with researchers, research institutions, funding bodies and industry partners across Ireland. The areas expressed in this document represent a living statement of the NCSC’s research and innovation interests. They reflect the challenges identified through a formal research needs development process, internal and external stakeholder engagement, the findings of the National Cyber Risk Assessment and the emerging priorities shaping the next National Cyber Security Strategy and wider Government and European Union policy.
-
NCSC Research Partnership Policy
The NCSC currently engages on an ongoing basis with:
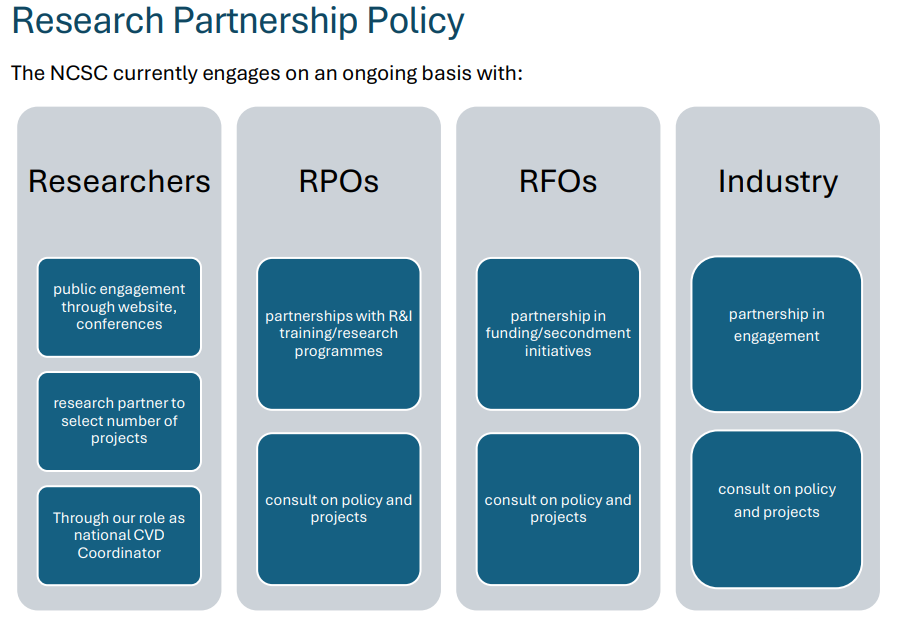 The NCSC Research Partnership Policy is to engage with researchers through institutional channels. The current structure of the NCSC does not support one-to-one Research Partnerships; however, we welcome requests for project partnerships and on occasion we may engage at a project level.
The NCSC Research Partnership Policy is to engage with researchers through institutional channels. The current structure of the NCSC does not support one-to-one Research Partnerships; however, we welcome requests for project partnerships and on occasion we may engage at a project level.
-
Protecting Against Business Email Compromise and
Payment Fraud Guidance
Business Email Compromise (BEC) is a type of cybercrime where attackers impersonate a legitimate business contact - often a company executive, supplier, or employee - to trick individuals into transferring money or sensitive data.
-
Draft Risk Managment Measure Guidance
The Draft Risk Management Measures (RMM) provide detailed guidance on the measures the NCSC believe will be the minimum required to meet the obligations of NIS2 for essential and important entities. The RMM are aligned with the Commission's Implementing Regulation for cross-border entities from the Digital Infrastructure and Digital Service Provider' sector. The RMM represent the minimum baseline of compliance and represent the 'what' organisations need to do.
-
Online account security – Plain English guide
This guide provides guidance in simple language on how best to protect and secure your online accounts, and reduce the risk of being hacked. It is approved by NALA, the National Adult Literacy Agency.
-
Online account security – Plain English guide, Irish Version
Slándáil cuntais ar líne – Sa treoir seo, tugtar comhairle i dteanga shimplí maidir le conas is fearr is féidir leat do chuntais ar líne a chosaint agus a dhaingniú agus an baol go haiceálfaí thú a laghdú.
-
Cyber security for small business
Cyber security is not just an information technology problem, but an integral part of any overall business strategy. This guidance document includes practical and evidence-based security measures to help protect your business against some of the most common threats in the area.
-
Quick Guide: QR Code Phishing and Scams
The NCSC has produced a cyber security quick guidance document on QR Code Phishing (Quishing) for the public. It is a non-technical guide to help you avoid QR Code scams and shows the steps you can take to protect yourself.
-
General Election 2024 Threat Landscape
This provides a high-level overview of current threats in the cyber domain relating to elections, and a risk assessment as relating to Ireland.
-
Denial of Service Attack Guidance
This guidance provides an overview of different DOS attacks, and a preparedness walk-through to assist in hardening your systems against such attacks.
-
National Cyber Emergency Plan
The plan outlines the process by which a National Cyber Emergency is declared, managed and co-ordinated. It ensures that everyone understands their roles and responsibilities during a cyber emergency, and that the Government's approach to serious cyber incidents is clearly explained and communicated to the public.
-
Cybersecurity for Political Organisations and Election Candidates
The twelve months from May 2024 will contain local elections, European Parliament elections, a general election, and potentially referenda. In order to assist those who may be running in any of these, and political parties as organising bodies for those running, the NCSC has published an updated guide on cyber security.
-
NCSC Seasonal Awareness
As we approach the busy Christmas period the NCSC would like to remind shoppers to be vigilant when online during this busy period. Cyber criminals will look to exploit consumers at this time of year which makes it more important than ever to keep yourself safe when online. The guidance document above will help you to secure your online identity this festive period.
-
Cyber Security Guidance on Generative AI for Public Sector Bodies
This guidance document, aimed at Public Sector Bodies outlines the main risks associated Generative AI, including how it could be abused by malicious actors. The document also provides advice on the secure use of Generative AI.
-
NCSC Multi Factor Authentication Guide
This is our user-friendly guide on Multi-Factor Authentication (MFA). Learn why it's essential, how it boosts your online security, which MFA is best for your organisation and easy ways to implement it across your online accounts.
-
Guidelines on Cyber Security Specifications (ICT Procurement for Public Service
Bodies)
These guidelines provide an understandable set of specifications that can be referenced by Public Sector Bodies when they are planning the procurement of ICT goods and services. It addresses a range of cyber security domains including organisational practices, supply chain security (including risks such as data leaks, supply chain breaches, and malware attacks), evaluation considerations, and attestation information that may be required from suppliers when procuring ICT goods and services throughout the Plan, Source and Manage phase of the procurement process.
-
Mobile Device Management for Public Sector Bodies
The Mobile Device Management Guidance builds upon the Cyber Security Baseline Standards and provides detailed guidance to Public Sector Bodies on the management and security of mobile devices within their organisation. It covers the threat landscape, risk assessment, procurement, management, security measures and vetting of third party apps.
-
NCSC Office 365 Secure Configuration Framework
The Secure Configuration Framework for Office 365 provide guidelines for optimally configuring Microsoft Office 365, with a specific on emphasis on security. The guidelines offer guidance and support to Irish Government Departments in configuring Office 365 to meet their compliance obligations and leverage the features and capabilities that are present within the service.
The framework provides an overview of the steps that provides specific actions that should be taken to set-up Office 365 optimally, from establishing the basic foundational security controls to key considerations around bring your own device (BYOD) controls. The framework empowers all organisations to take steps to improve their security posture.
As we approach the busy Christmas period the NCSC would like to remind shoppers to be vigilant when online during this busy period. Cyber criminals will look to exploit consumers at this time of year which makes it more important than ever to keep yourself safe when online. The guidance document above will help you to secure your online identity this festive period.
-
Cyber Security Baseline Standards Self-Assessment Form
The Cyber Security Baseline Standards Self-Assessment form is a checklist that Public Service Bodies can use internally to assess their cyber security posture against the Cyber Security Baseline Standards. The self -assessment form provides specific self-assessment guidance and support to each organisation for each of the categories and sub-categories identified in the Cyber Security Baseline Standards. Security control assessments can be challenging and this form provides a ready-made solution across the various operating environments and organisational frameworks of the Public Service.
-
Quick Guide: Phishing
This cyber security quick guidance document on phishing has been produced by the NCSC to help you to avoid being phished, spotting the giveaway signs of phishing e-mails, and what to do if you think you've already clicked the attackers bait.
-
Securing Operational Technology
Securing Operational Technology provides guidance to organisations about the risks associated with OT and the best practices they should implement in order to use it securely.
-
NCSC Cyber Vitals Checklist
The NCSC Cyber Vitals Checklist, aimed at an organisation's senior management & security teams, is the priority actions that can be taken, to check the organisations cybersecurity posture, during times of heightened cyber threats. It is not intended to replace more detailed guidance, such as the OES Guidelines or Cyber Security Baseline Standards, but rather acts as a pulse check, and a prioritised list of key actions to take, in light of a heightened threat.
-
Cyber Security Baseline Standards
The Baseline Security Standard, based on the NIST Cyber Security Framework, provides the baseline measures that Public Sector Bodies should implement in order to secure their networks.
The Baseline Standards are intended to create an acceptable security standard and form a broad framework for a set of measures which can be revised over time. The Baseline Standards model follows a holistic and comprehensive approach to the issues related to Cyber Security which combines the best of various standards to address the needs of key stakeholders.
-
NIS Compliance Security Guidelines for OES
The NIS Compliance Security Guidelines, establishes a set of security measures designed to assist OES in meeting their network and information system security and incident reporting requirements under Regulations 17 and 18 of the NIS Regulations. These guidelines are both technology neutral and non-sector specific to allow OES in different sectors adapt these to meet their needs, and to evolve their sector specific response along with technological advances and business requirements.
-
Quick Guide: Cyber Security for Schools
This quick guide will highlight the cyber risks posed to schools and the key priority measures to consider to mitigate against these risks.
-
Quick Guide: Ransomware How to #BreakTheChain
Ransomware operators are not only interested in critical infrastructure, ransomware attacks can affect all types of organisations, both large and small. This quick guide is for organisations to understand the steps in a Ransomware Attack Chain, and more importantly how good cybersecurity practices will allow you to stop an attacker and #BreakTheChain.
-
Quick Guide: Cyber Security Best Practice for Electoral Candidates
This cyber security best practice quick guide has been produced by the NCSC to assist electoral candidates in implementing key priority preventive measures that can help to reduce the likelihood of them becoming a victim of a cyber-attack and the negative impacts that may result.
-
Working From Home Security Advice
With remote working becoming part of our day to day life, it is important that you ensure your home office matches the level of security you would expect to find in your professional office environment. This detailed guidance document covers some important steps you can take to achieve this.
-
12 Steps to Cyber Security for Businesses
This detailed guidance is intended to be used by businesses as a suggested activity plan which may be undertaken on a month-by-month basis over a suggested 12 month period to improve cyber resilience.
