Phishing
For the theme of phishing in this year's ECSM, the spotlight will be on the ever present and fraudulent phishing emails used by attackers to lure people into disclosing personal details or clicking on malicious links.
Phishing e-mails remain the primary method used by cybercriminals to gain unauthorised access to a computer or network, with hackers continuing to design smarter and more sophisticated examples of them in the hope of gaining peoples trust and pressuring them into acting without thinking.
By using e-mails, attackers can reach huge numbers of people directly whilst hiding within the large number of e-mails people receive each day. These emails may look genuine, and the sender will usually claim to be a person or organisation that you are familiar with to make it easier for t hem to gain your trust. As these e-mails become more and more convincing, they can be difficult to spot and are designed to get you to interact with the message without thinking. The attacker aims to take advantage of people's social instincts, such as being helpful and efficient or their emotions such as fear or anger.
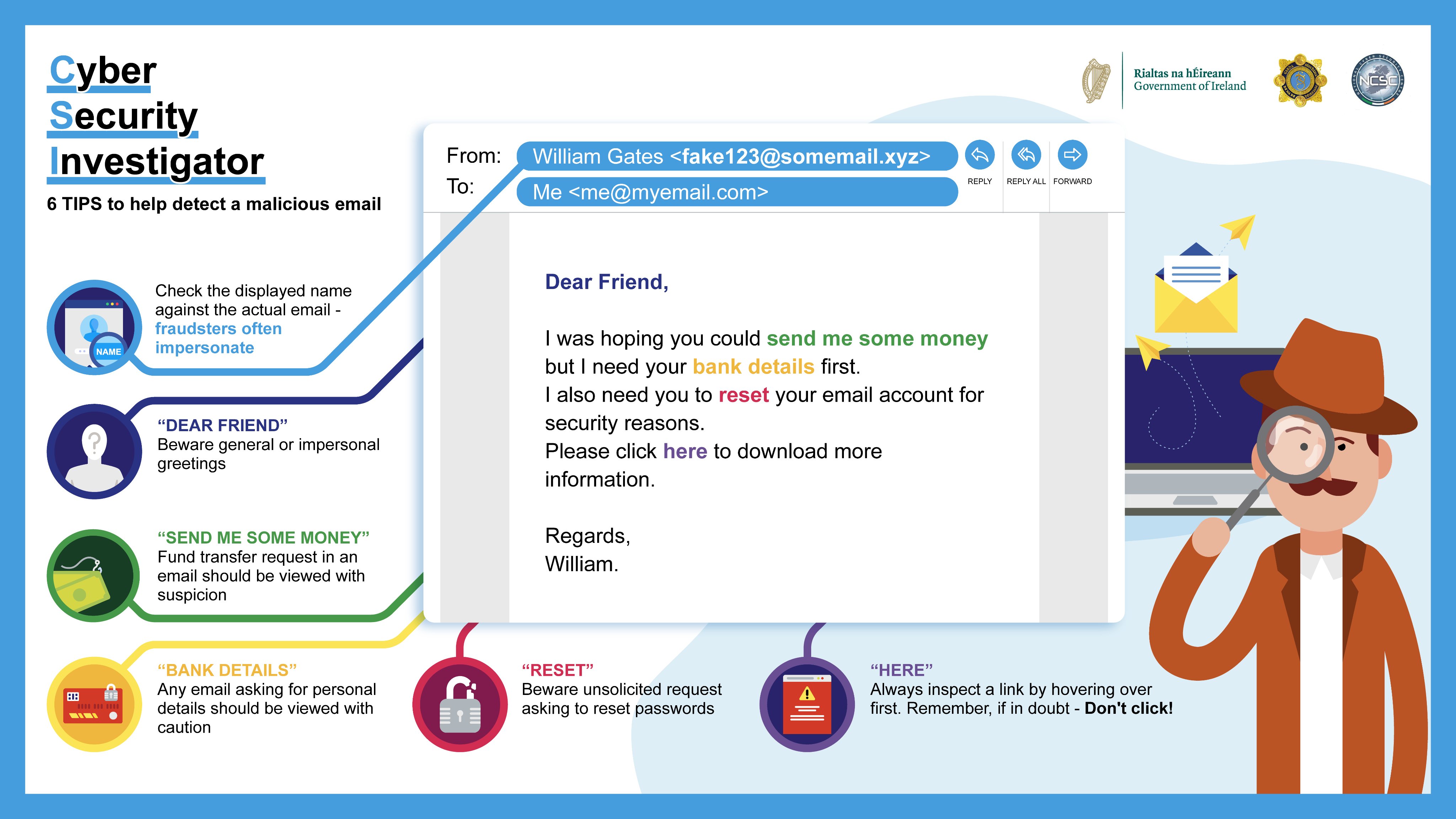
Criminals will check the internet for peoples publicly available information to make their phishing e-mails more convincing. You can still stay one step ahead of them by remembering to scan for one or more of these giveaway phishing signs that could signify you are being targeted by a phishing e-mail.
Please see our guidance section for additional resources.
Quick Guide: Phishing
This cyber security quick guidance document on phishing has been produced by the NCSC to help you to avoid being phished, spotting the giveaway signs of phishing e-mails, and what to do if you think you've already clicked the attackers bait.